Tailored Expertise For Your Mission
Advanced IT consulting and security for various sectors.
Advanced Security & Zero Trust Architecture
DoD Unified Communications
Advanced Project Management




Zero Trust Framework: Continuous authentication, microsegmentation, and least privilege access.
CSfC Integration: Secure commercial solutions for classified operations.
Cross-Domain Solutions: Secure data transfer between networks of varying classification.
Enhanced Identity & Access: Multi-factor authentication and strict identity verification.
Endpoint & Supply Chain Security: Continuous risk assessments and endpoint protection.
Real-Time Threat Monitoring: Rapid detection and response via integrated threat intelligence.
Insider Threat Mitigation: Robust auditing to neutralize internal risks.
Compliance & Risk Management: Adherence to DoD standards and best practices.
DoD UC Requirements: Adhere to DoD Instruction 8100.04 for voice, video, chat, and presence.
Approved Products List (APL): Leverage DISA's APL for secure UC solutions.
DISA UC Approved Solutions: Utilize certified platforms for voice, video, chat, and conferencing.
Secure Mobility & Tactical Communications: Enable secure UC on mobile and tactical devices.
Quality of Service (QoS) Assurance: Enforce strict QoS policies for reliable, uninterrupted communications.
Radio over IP (RoIP): Deliver secure, mission-critical radio communications over IP.
Mass Notification Systems: Ensure rapid, secure mass alerts for emergency and operational communications.
PMP-Certified Leadership: Our PMP-certified team drives projects with industry best practices.
Strategic Alignment: Ensure projects meet mission objectives and stakeholder needs.
Cost & Schedule Control (EVMS): Leverage Earned Value Management to monitor budgets and timelines.
Risk Mitigation: Proactively identify and manage risks for sustained project success.
Task Structuring (WBS): Develop detailed Work Breakdown Structures to organize and assign responsibilities.
Integrated Scheduling (IMS/IMP): Coordinate milestones and deliverables with a unified master schedule and plan.
Regulatory Compliance: Adhere to essential standards and guidelines for quality and accountability.
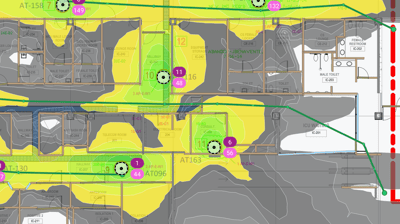




Mission-Critical Architecture: Design networks that meet DoD operational needs.
ASLAN Implementation: Deploy secure, reliable local networks for defense operations.
Advanced Routing & Switching: Optimize performance with modern, efficient infrastructure.
Wireless Solutions: Enable robust, flexible wireless connectivity for mobile operations.
Software-Defined Networking (SDN): Streamline network management and scalability.
Real-Time Management: Monitor network performance proactively for maximum uptime.
Compliance & Standards: Adhere to DoD standards and DISA guidelines for secure operations.
Networking & Infrastructure
Data Center & Cloud Solutions
DoD Cloud Strategy: Implementation of hybrid, multi-cloud, and edge solutions guided by Zero Trust principles.
JWCC: Secure cloud integration aligned with JWCC standards and leveraging leading providers.
Impact Levels: Cloud architectures designed to comply with DoD IL2–IL6 security requirements.
Zero Trust: Enforcement of identity-based access controls and continuous monitoring across deployments.
Data Strategy: Adoption of robust data governance and AI-driven analytics to maximize strategic value.
JIE: Integration of on-premise, cloud, and edge systems into a unified IT infrastructure.
MPE: Enablement of secure, cloud-based collaboration with coalition partners.
EITaaS: Delivery of IT-as-a-Service solutions ensuring mission-critical uptime.
IT Consulting & Mission Assurance
Strategic IT Consulting: Tailor technology solutions to align with mission objectives.
Mission Assurance: Ensure system resilience and operational readiness.
Risk & Compliance: Adhere to RMF, DISA, and DoD standards for secure operations.
IT Roadmap & Transformation: Develop comprehensive strategies for digital modernization.
Security & Infrastructure Assessments: Identify vulnerabilities and optimize defenses.
Technology Integration: Seamlessly incorporate advanced IT and security solutions.
Training & Support: Empower teams with essential skills and ongoing guidance.
Continuous Improvement: Drive iterative enhancements and innovation.
Veteran Owned
SecureBine Solutions specializes in advanced security, networking, and IT consulting, providing tailored solutions for commercial and government clients across the Indo-Pacific region.


25 Years of Proven Expertise
Our team of highly experienced, security-cleared professionals leverages decades of industry knowledge and rigorous training to deliver robust, mission-critical solutions that ensure unmatched protection and operational excellence.
As a Veteran Owned Small Business, we combine deep IT expertise with a proud military heritage to deliver secure, mission-critical solutions. Based in Korea, we leverage our deep local insight and extensive experience throughout the Indo-Pacific region to provide effective, strategic support.
Contact Information
Support
email: sales@securebine.com
Korea: +82-10-4461-1820
© 2025. All rights reserved.


US: +1-844-727-5496
